by Solution
RFID creates choke points at fixed read points. Our scan-free solutions provide continuous visibility with the lowest cost infrastructure, delivering real-time supply chain intelligence while minimizing errors, reducing waste, and driving ROI across enterprises.
- Automated Cycle Count
- Automated Receiving
- Reusable Asset Tracking
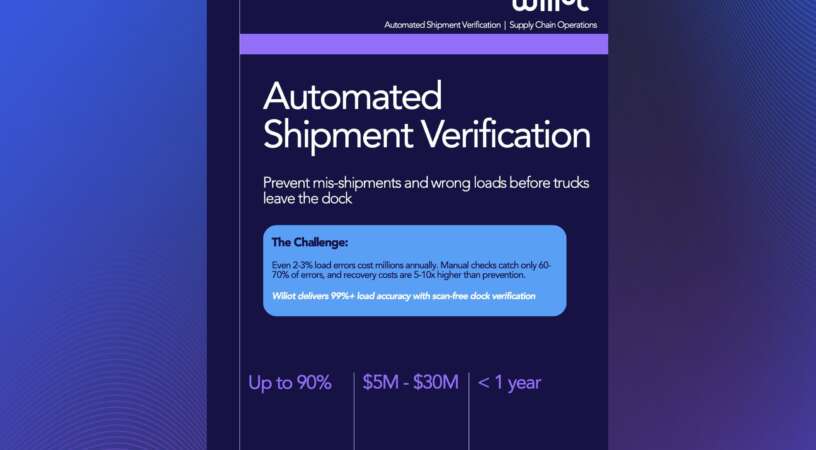
- Automated Shipment Verification
- Temperature Monitoring
Over 180,000 assets located and millions of pounds saved in new

by Industry
Explore Wiliot for retail, logistics, and quick service restaurants—improving operations with real-time visibility
The Basics
Dive into educational content covering Wiliot’s technology, industry trends, and use cases across multiple sectors
Other Resources
Access case studies, podcasts, and white papers for deeper insights into Wiliot’s impact and solutions
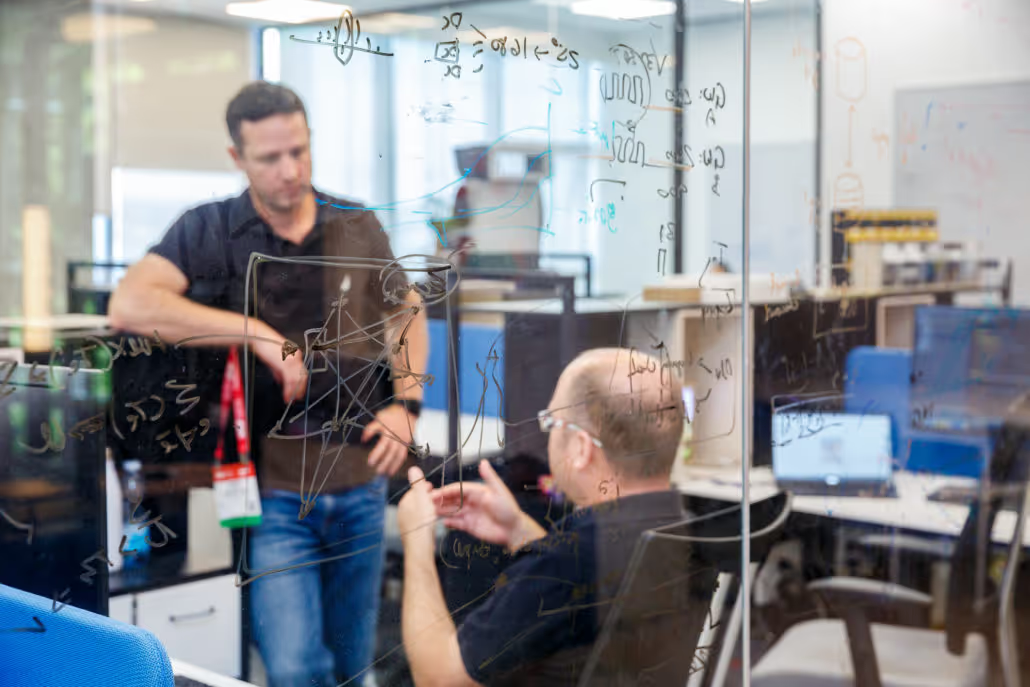
About us
Learn about Wiliot’s mission, awards, certifications, and vision for transforming industries with Ambient IoT
News
Stay current with our announcements, press releases, articles, and insights from industry experts and analysts
Events
Find upcoming events, webinars, and replays of key sessions featuring Wiliot’s experts and partners




.svg)
.svg)


%20(1).jpg)
















.jpg)




.webp)